Picture walking into a manufacturing facility where every connected device flows through secure, purpose-built network infrastructure. This isn’t just technological advancement, it’s the foundation of cyber resilience in an era where manufacturing faces unprecedented threats.

Ransomware attacks surged 46% across manufacturing and other industrial sectors from Q4 2024 to Q1 2025. The question is no longer if your facility will be targeted, but whether your network infrastructure can protect you when it happens.
The manufacturers who succeed in the coming years won’t necessarily be those with the most expensive security tools. Instead, they will be the ones who understand that true cyber resilience starts with the network itself. Adding more cybersecurity tools on top of outdated infrastructure isn’t enough, security must be designed into the foundation. A purpose-built network architecture treats every device as part of a coordinated defense system rather than a potential entry point.
The Manufacturing Cybersecurity Crisis: Why the Industry is Under Attack
Manufacturing has become the primary battleground in the cybersecurity war. The sector has been the number one target for ransomware groups four years in a row, accounting for 22% of all reported attacks between April 2024 and March 2025.
This concentration isn’t a coincidence—it’s the result of cybercriminals deliberately targeting industries where valuable data meet vulnerable systems.
Every minute, over 152,200 IoT devices connect globally, each one representing both operational opportunity and security risk. For manufacturers, that includes not just computers but also programmable logic controllers (PLCs), human-machine interfaces (HMIs), sensors, robots, and other industrial IoT systems that keep production lines running.
At the same time, attacks are becoming more sophisticated. Nearly half of manufactures (44%) expect to face AI-enhanced threats, but only a third (32%) feel prepared for them. These AI-driven attacks identify vulnerabilities faster than humans can patch them, launching adaptive, coordinated campaigns that overwhelm traditional defense.
Understanding Manufacturing’s Unique Vulnerabilities
The threat landscape is amplified by characteristics unique to manufacturing environments:
- Legacy System Challenges: Many facilities still rely on older equipment that receives minimal or no security updates, creating persistent vulnerabilities that modern defenses can’t easily address.
- Operational Technology (OT) Convergence: Integration between production and business systems introduces new pathways for attackers to move from accessible IT systems into critical OT environments.
- 24/7 Operational Pressure: Continuous production leaves little room for downtime, making regular patching and updates difficult.
- High-Value Intellectual Property: Designs, proprietary processes, and operational data make manufacturers high-value targets.
- Supply Chain Interdependencies: One in five attacks originates from compromised suppliers or contractors with trusted access..
The result is that a single compromise can halt production, jeopardize safety, and cause downtime costs that reach thousands, or even hundreds of thousands, of dollars per hour.
Why Network Infrastructure Is Your First Line of Defense
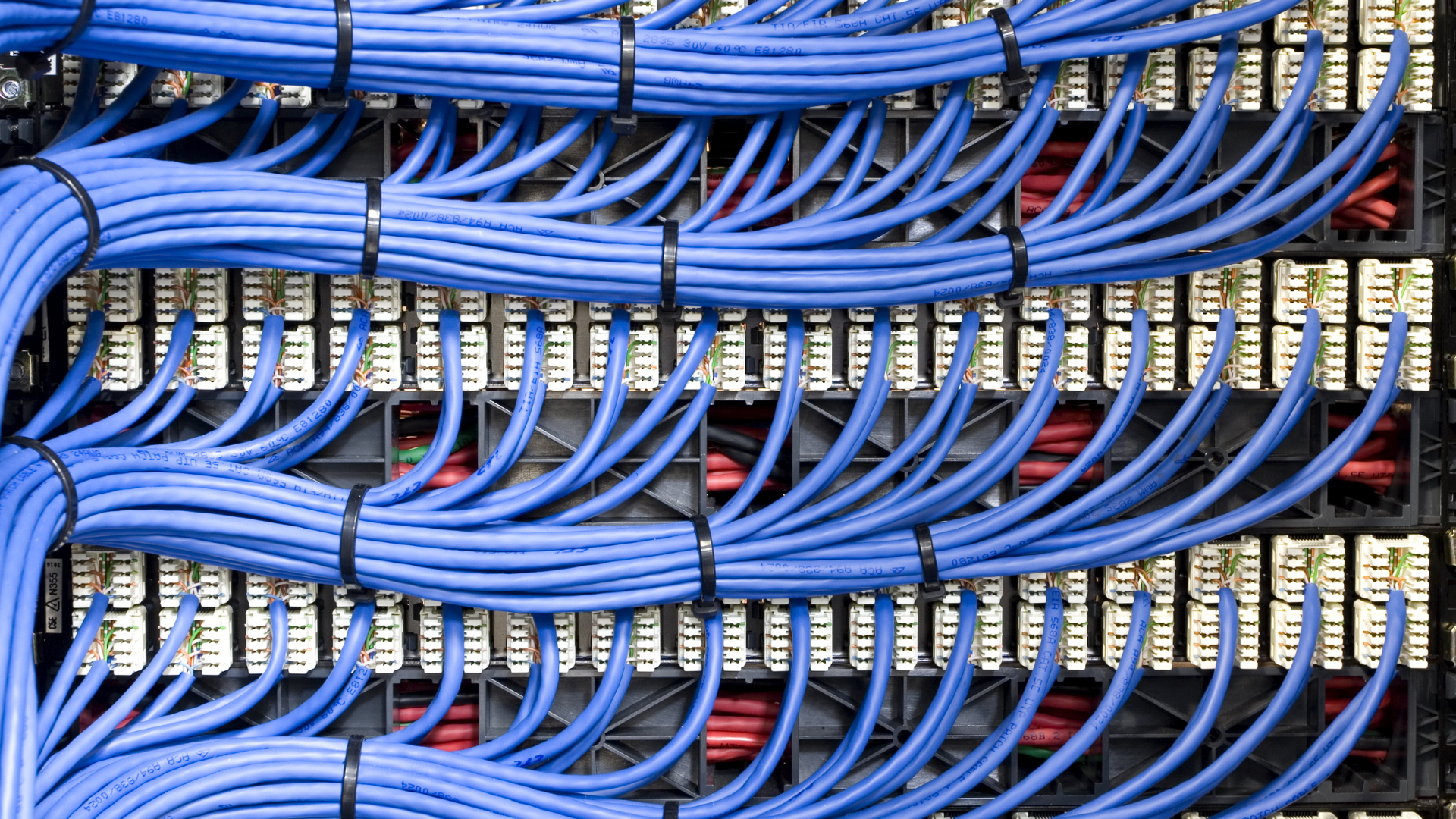
Given these risks, manufacturers must rethink how cybersecurity is implemented. Security cannot be an overlay; it has to be built into the network itself. A secure, well-architected infrastructure transforms the network from something threats exploit into something that actively contains them.
Fiber-Optic Security Advantages
Fiber-optic networks provide inherent security benefits perfectly suited for manufacturing environments. Unlike copper systems that emit electromagnetic signals which can be intercepted, fiber transmits data as light pulses and is extremely difficult to tap without detection. Fiber also resists electromagnetic interference, which is vital in facilities filled with heavy machinery and welding equipment.
Network Segmentation
Segmentation ensures that even if an attacker breaches one zone, they can’t move freely across the network.
Effective strategies include:
- Isolating critical OT systems from corporate IT networks
- Creating separate zones for production lines
- Monitoring all traffic between segments
- Enabling rapid isolation capabilities during an attack
Zero Trust Architecture
Zero trust replaces the idea of a trusted internal network with “never trust, always verify.” This means every access request—no matter where it originates—is authenticated, monitored, and continuously revalidated. In manufacturing, this approach must balance strict security controls with the operational realities of safety-critical systems.
Redundancy and Failover
A resilient network doesn’t just block attacks—it keeps operations running when disruptions occur.
Redundancy includes:
- Multiple independent network paths for critical communications
- Automated failover switching to backup networks within seconds
- Geographically distributed equipment preventing single points of failure
- Backup systems maintaining basic capabilities if primary networks are compromised
Continuous Monitoring Integration
Network-embedded monitoring provides:
- Real-time visibility into all communications and device behaviors
- Behavioral analysis detecting subtle compromise indicators
- Traffic pattern analysis identifying unauthorized lateral movement
- Automated threat detection responding faster than human analysis
Aligning with Proven Frameworks: NIST and CISA Best Practices
Manufacturers don’t need to start from scratch. The NIST Cybersecurity Framework Manufacturing Profile and CISA guidelines provide practical approaches designed for the unique realities of manufacturing challenges. Unlike generic frameworks, it acknowledges operational realities of continuous production, safety considerations, and supply chain interdependencies.

Key areas include:
1. Asset Inventory and Classification:
- Traditional IT assets (servers, workstations, network equipment)
- Operational Technology assets (PLCs, HMIs, sensors, actuators, specialized software)
- Classification based on operational criticality and connectivity
- Discovery of “shadow IT” and undocumented connections
Effective inventory often reveals devices temporarily connected for projects but never properly secured, creating unknown attack vectors requiring immediate attention.
2. Multi-Factor Authentication (MFA) for Manufacturing:
- Workers wearing protective equipment interfering with biometric scanners
- Environments where mobile devices may not function reliably
- Emergency situations requiring immediate system access for safety
- Integration with industrial workflows and operational procedures
3. Incident Response for Continuous Operations:
- Rapid safety risk assessment protocols
- Decision trees for production continuation versus shutdown
- Communication ensuring cybersecurity and operational teams coordinate effectively
- Preservation of evidence while maintaining customer commitments
4. Vulnerability and Patch Management:
- Extended lifecycles of industrial equipment receiving limited updates
- Testing protocols validating functionality after security modifications
- Change management preventing operational disruptions
- Risk-based prioritization considering threat likelihood and impact
5. Employee Training for Industrial Environments:
- Recognition of industrial-specific phishing referencing equipment and procedures
- Understanding safety implications of cybersecurity incidents
- Practical security maintenance during normal operations
- Clear incident reporting integrated with safety procedures
Strengthening Security with Edge Computing
As manufacturing becomes more connected, edge computing plays an increasingly important role in both operational efficiency and cybersecurity.
By processing data locally rather than sending it to distant cloud servers, manufacturers reduce latency, limit exposure, and maintain control over sensitive information.
Edge environments allow:
Local Data Processing Security:
Edge computing processes sensitive manufacturing data locally rather than transmitting across potentially vulnerable networks to distant data centers. This means proprietary production data, quality control information, and operational analytics remain within facility boundaries, reducing exposure and eliminating privacy concerns.
Real-Time Threat Detection:
Local processing enables immediate threat detection impossible with cloud-based systems accounting for network latency. Edge-based security monitors traffic, device behaviors, and operational patterns continuously, identifying and responding to anomalies within milliseconds rather than minutes required for cloud analysis.
Operational Continuity During Disruptions:
Manufacturing facilities with robust edge capabilities maintain production during network outages, cyber-attacks affecting wide area networks, or incidents compromising external connectivity. This resilience ensures local problems don’t cascade into production shutdowns.
Data Sovereignty and Compliance:
Edge computing enables complete control over data processing and storage locations, ensuring compliance with localization requirements and reducing exposure to foreign jurisdiction access laws. Manufacturers keep sensitive data within local boundaries unless explicitly authorized.
Future-Proofing Manufacturing Security
Tomorrow’s cybersecurity landscape will be fundamentally different, driven by technological advances creating new opportunities and unprecedented threats. Forward-thinking manufacturers build adaptive capabilities responding to threats not yet imagined while maintaining operational efficiency.
Future-ready strategies include:
AI-Driven Defense
AI transforms both defense and attack methodologies. Defense systems analyze network traffic and device behaviors at impossible scales for human analysts, learning normal patterns to detect facility-specific anomalies. However, cybercriminals develop AI-enhanced attacks adapting tactics real-time and exploiting vulnerabilities faster than traditional responses.
Manufacturers must implement continuously learning systems rather than static security rules, requiring infrastructure supporting machine learning workloads and personnel training for AI-enhanced security management.
Supply Chain Security Integration
Evolving regulations require manufacturers to verify cybersecurity practices of all suppliers and partners with network access. This includes comprehensive vendor assessment programs, contract requirements mandating security standards, and ongoing monitoring detecting supplier incidents before they impact operations.
Regulatory Compliance Evolution
Governments increasingly recognize manufacturing as critical infrastructure, implementing stringent requirements including mandatory incident reporting, specific security standards, regular compliance audits, and potential executive liability for inadequate cybersecurity.
Adaptive Security Architecture
Future manufacturing requires adaptive architectures automatically adjusting protection based on threat conditions and operational requirements. This includes automated threat response containing incidents without human intervention, dynamic access controls adjusting permissions based on risk levels, and self-healing networks maintaining operations when components are compromised.
Building Resilient Manufacturing Operations: The Path Forward

The cybersecurity challenges facing manufacturers in 2026 are complex—but manageable for those who treat cybersecurity as a core business function, not an afterthought.
Purpose-built network infrastructure is the foundation of this resilience. Fiber-optic networks provide secure, interference-free transmission; segmentation and zero trust limit breach impact; and edge computing maintains local control even when external systems fail. Together, these create an ecosystem designed for both security and operational excellence.
The manufacturers gaining a competitive edge today are those investing in adaptive architectures that evolve with emerging threats, AI-driven security systems, and growing regulatory demands.
Manufacturing security isn’t just about stopping attacks—it’s about ensuring your business thrives in a connected world where digital capabilities drive competitive advantage.
Transform Your Manufacturing Security with WIN Technology
At WIN, we combine cybersecurity expertise with purpose-built network infrastructure designed specifically for manufacturing environments. Our AI-ready fiber network, regional edge centers, and comprehensive managed IT services create a resilient foundation for modern operations.
Talk to a WIN specialist to explore how secure network infrastructure can strengthen your operations and prepare your facility for 2026 and beyond.
